Security and Sharing
With electronic documents we can have a greater level of security and control than is possible with paper. First a word of warning, security for your IT systems is a massive and important topic and should implemented with the greatest of care. Before considering any vendor of technology components for security it is fundamentally necessary to consider overall requirements and policies. Too readily vendors will sell you what they want, not what you need. They will rarely accept realistic liabilities, and therefore the onus on implementing their components in a secure way rests with the purchaser.
As covered in the above warning for this guide I will give you a summary of some of the security methods available and then concentrate on only those that directly benefit the use of electronic documents and forms discussed in the previous sections of this guide. The sections will be;
- Login & Passwords
- Roles and Your Organization
- Access Control Lists
- Authorisation
– E-signatures, digital signatures - Watermarks
- Digital Rights Management
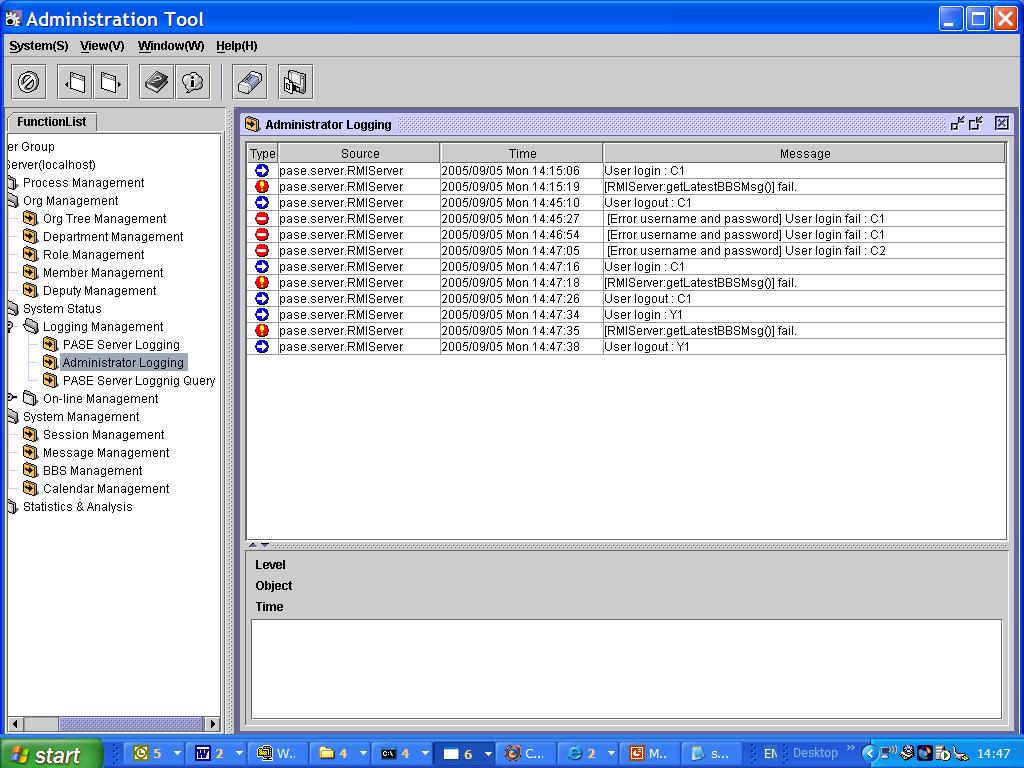
Login and Passwords
The first step is for your user to identify themselves. This requires authentication. The three factors of authentication are:
– Something you have (a smart-card, or a token)
– Something you know (a PIN or a Password)
– Something you are (biometric data)
Your organisations security policy will state which of these are required, many organisations will use a password (something you know) only. Increasing your security level is now much easier and cost effective. Implementing Public Key Infrastructure (PKI) (something you have) is very popular, more on this later. Also many laptops aimed at business use now come with fingerprint readers, (something you are). These techniques, implemented correctly can give you confidence that the person using the system is who they should be.
All this is generic IT security information so when it comes to implementing your electronic document systems look out for concepts like “Unified Login” this is available on most IT systems and means that you can use the same security and identification system for all your applications including Document Management. This feature can usually be switched on or off and whether you use it is dependant upon you policy, the benefit of using unified login is that you can implement a higher security level than is available as standard with the product. But by not using it will give you separation between your document management system and other systems giving greater portability. Unified logon with modern products uses a standard called LDAP (lightweight directory access protocol) so that your standard directory services system is used (Active Directory for example). LDAP can also be useful if you do not use unified logon as it can be used to transfer user information between your different systems to reduce typing errors.
Roles and Your Organization
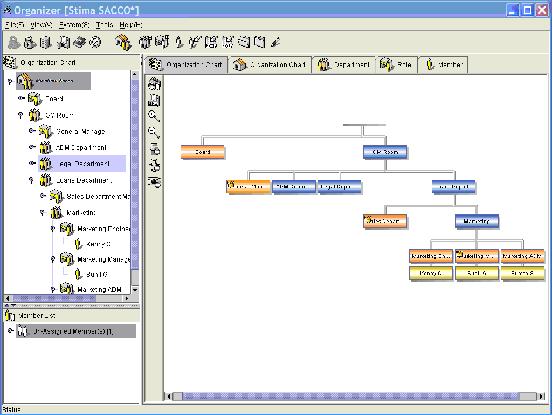
Access to most of the information we have discussed so far in this guide is dependant upon the job function of your employees. Because of this it is much simpler to implement a document security system based on Roles rather than individuals. We have already discussed how we can replace paper forms with electronic forms, now if you take a look at the form being used inside your organization and you will see how many of these require authorization by the originator’s Manager. To make this process simpler the system should know your companies organization chart so that it knows who reports to who. The real benefit from this approach is when one of the managers moves from one department to another, if your security is based on them as an individual how long will it be before he stops receiving expense claims for his previous staff members and how long will it be before he has full access to all the information needed for his new role?
So when looking for a system make sure it has role based security and an organization manager.
Access Control Lists
Access Control Lists (ACL) are the standard method of implementing security to your electronic documents. These lists can be added to a document a folder or sub folders and contains the user name, the role, the department or the group that have access to the documents. This access is typically read, write or administrator. These rights are hierarchical, i.e. if you have write access you also have read access and if you have supervisory rights you can read and write. More sophisticated systems will also include other functions such as copy or print in the ACL.
There should also be a different Access Control List for the actual document and the supporting information (Meta Data). To show the importance of this lets look at the Document that details the Terms and Conditions relating to a product your organization sells. The content of the document may have been written by your company lawyer but the life of the product is managed by the Product Manager. As the obsolete date is held in the meta data the product manager needs to change this, in this example the Lawyer will have write access to the document but only read access to the meta data and the product manager will have write access to the meta data but only read access to the document.
Authorization
The type of authorization is dependent on the importance to your organization of the transaction or approval. Therefore security levels of authorization are needed. These fall into two main categories and these are often confused. The first is e-signatures or electronic signatures. The definition of this is; “A method to associate a record or action with a person” and this is the most commonly used authorisation used in the types of systems we are describing in this guide. As an example let’s look at a manager authorising payment of the expenses of one of their staff member. The manager will look at the electronic form and decide if the payment should be made, because the system will log and record all actions on the system, should this payment be disputed later then the form together with the log will prove that the manager authorized the transaction. To make sure that the manager did not accidentally make the authorization it is common to make them take some sort of positive action, tick a box marked “approved” for example. If more action is needed then the manager may have to tick the box AND enter a password before the transaction can be authorized.
The second authorization category is Digital Signatures. The simple definition being; “A method to associate a record or action with a person”. There has been a lot of discussion about legal admissibility of electronic transactions and in most places in the world it is Digital Signatures that comply and so it is expected that this will be the case here later in the year. To implement Digital Signatures you will need stronger proof of who the user is than a simple password and so will have to implement PKI or similar.
Watermarks
As discussed in the previous section watermarks can be automatically added to a document when published, these water marks can be “Confidential” or “not for distribution” leaving the user no doubt that this document should not be copied. These watermarks can also contain dynamic information such as User Name and date and time accessed. If then one of your documents does find its way into the public domain then the source of the leak can quickly and easily be identified.
Digital Rights Management
Above we saw how we could trace a security breach after it had occurred, if you feel that you cannot risk any of your sensitive information to fall into the wrong hands but you still need authorized users access then you should consider implementing Digital Rights Management. The origins of this technology comes from the Media Industry (music and film) who are loosing Billions of Dollars due to piracy. If you have an iPod and have bought music from iTunes you will have noticed that it is impossible to play that tune on another computer and you are only allowed to make five copies for your own personal use. Also now with movies if you want to watch a movie you no longer have to drive down to the local rental store, you can download the film. As with the music you cannot make copies of the film or play it on another computer, also as with the rental copy I can only watch it for a few days, after this time the film is automatically deleted. This is now available to protect your documents, in the same way as the other media the document cannot be copied and will be deleted after a pre-determined time period. In addition the DRM software will prevent the user from printing or using the copy and paste function.